Table of Content
This blog post announces the September 2021 Update for Bright.
We added some new features and product enhancements that will make your experience even better.
New Features:
Okta SSO provisioning
Now you can easily sync up the users and groups between your Okta application and Bright organization.
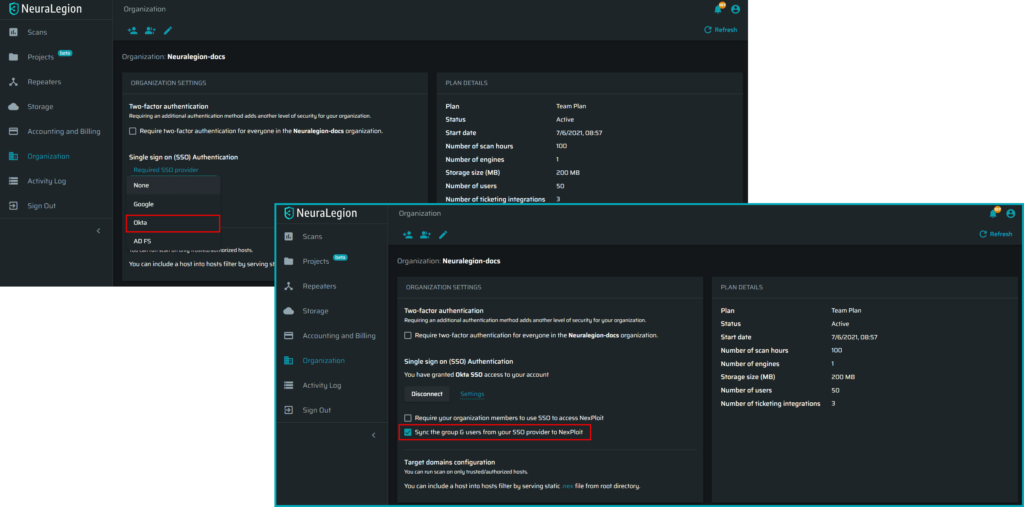
Check out the docs!
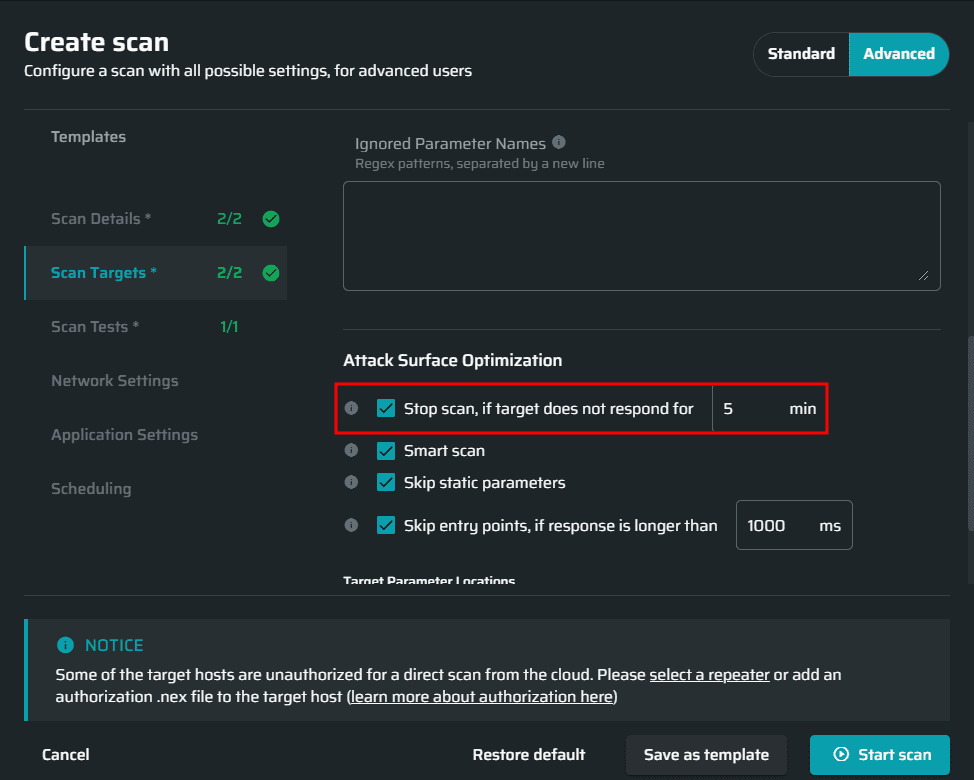
Global timeout for scans
We are here to help you save your time! If for some reason the scan target does not respond anymore, you don’t need to wait for a long time while all the scan tests are being sent into the void! Simply use our new feature to stop the scan automatically when the target is not responsive.
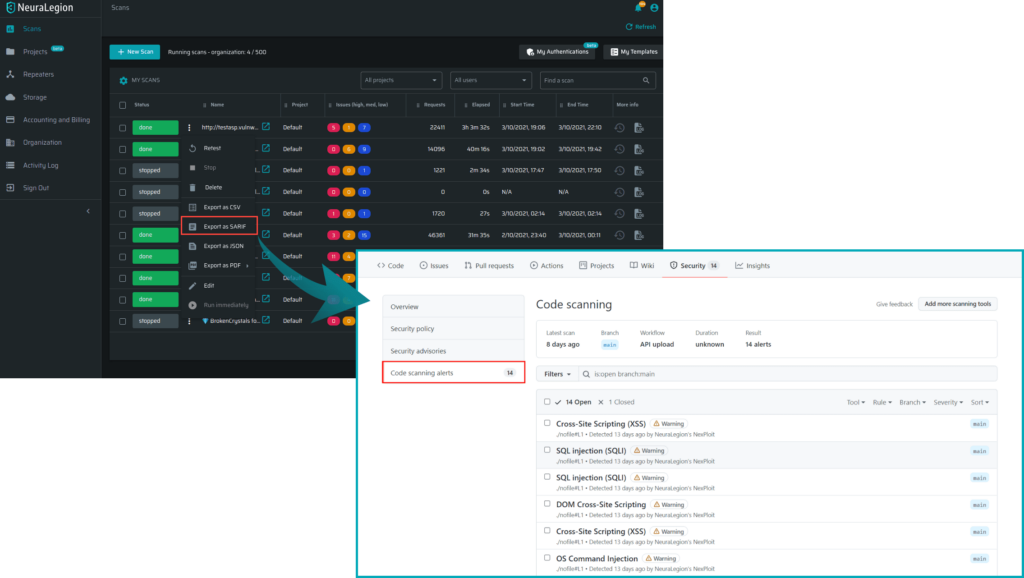
Integration with GitHub SARIF reports
Now you can manage all found issues from Code Scanning Alerts on GitHub.
Export Entry points list as CSV
We added the possibility to download all discovered entry points as CSV to help security teams analyze the scan results better.
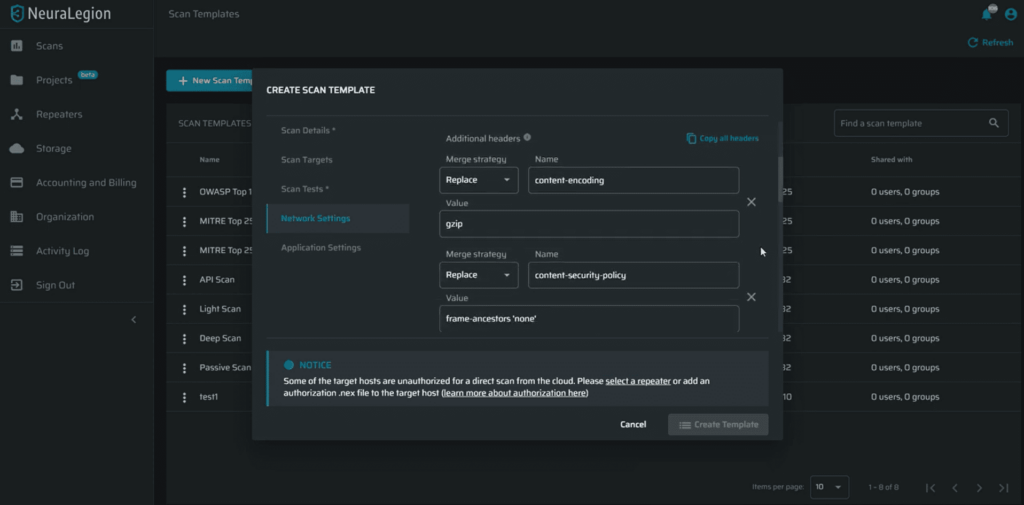
Advanced internal/external proxy configuration for the Repeater
From now, when scanning with a Repeater, you can proxy the internal (to your local network) and external (to our cloud) traffic separately.

Improvements:
Speed improvements for scans with a Repeater
Speed up when scanning with a Repeater!

Request/Response correlation IDs in Engine logs
You can now easily find the relevant response to a request by its ID!

UI stability improvements
Check out our new schema editor and other UX improvements to make your experience better!