What is OWASP ZAP?
OWASP Zed Attack Proxy (ZAP) is a free security tool actively maintained by international volunteers. It automatically identifies web application security vulnerabilities during development and testing. Experienced penetration testers can use OWASP ZAP to perform manual security testing.
Learn more in our detailed guide to owasp api top 10.
In this article:
8 Key Concepts and Features of the ZAP Scanner
1. Active Scan
Active scanning uses known attacks to identify potential vulnerabilities, which means it can only find specific vulnerabilities. Active or automatic vulnerability scans cannot find errors in application logic. It is possible only while conducting a manual audit.
2. Passive Scan
By default, ZAP scans HTTP requests and all responses sent and received from your application. Passive scanning does not affect their content. You can add tags or alerts to inform you about any potential errors. While this option is enabled by default, it is also possible to configure it.
3. OWASP ZAP Fuzzer
OWASP ZAP lets you use a fuzzer that sends many unexpected or incorrect data to a tested application. You can create your own payloads, use any of the built-in payloads, or download the payloads add-ons provided by the ZAP community.
4. OWASP ZAP API
OWASP ZAP provides an API that accepts JSON, XML, and HTML. The API’s functionality is explained on a web page, specifying that the default allows only the machine running ZAP to connect to the API. However, you can use the configuration options to allow other machines to contact the API.
5. WebSocket Testing
WebSockets are highly pervasive across applications. ZAP lets you easily intercept, analyze, or tamper with the WebSocket traffic between client and server. You can access the WebSocket Message editor by going to the ZAP Menu, choosing Tools, and then selecting WebSocket Message Editor. Use the editor to tamper with the Direction, Opcodes, or the WebSocket message before it is sent back to the server.
6. JAX Spidering
You perform AJAX spidering during a penetration test to identify requests on an AJAX-rich web application. You cannot identify these requests with a standard spidering tool. You can access the AJAX spidering window by going to the menu bar, choosing Tools, and then selecting AJAX Spider (on). This tool includes configuration parameters like maximum depth to crawl, maximum duration, maximum crawl states, and other options to help you prevent infinite crawling.
7. Scan Policy Management
ZAP lets you compose a scan policy according to specific requirements for each application. You can find the Scan Policy Manager under the menu bat. Go to Analyze, and then choose Scan Policy Manager.
Penetration testers need to optimize this scanner according to the target application’s abilities to keep up with the app’s operational performance and prevent DoS. While creating scan policies, you must consider the scanner machine’s bandwidth and processing capabilities.
You can alter a scan policy to exclude or include the test to perform. ZAP also lets you configure the definition of parameters such as:
- Threshold—the likelihood of flagging a potential vulnerability
- Strength—the number of requests for each of the tests
Penetration testers usually need to test the scenarios they might frequently encounter across the target application. ZAP lets you design a custom scan policy that you can export as a template. You can import the scan policy back into ZAP and reuse it.
8. ZAP Marketplace
ZAP Marketplace includes free and open source add-ons written by the ZAP team as well as the community. These add-ons enable you to extend the functionality of a ZAP implementation. You can browse the marketplace and download add-ons by going to the toolbar, clicking on the Manage Add-ons button, and then choosing the Marketplace tab.
Related content: Read our guide to owasp mobile top 10.
OWASP ZAP Tutorial: Install and Configure OWASP ZAP
ZAP provides installers for Linux, Mac OS/X, and Windows. The download page also provides Docker images.
Choose the appropriate installer
Go to the download page and install ZAP for the system you intend to perform penetration testing on.
Here are the requirements for ZAP and each installer:
- ZAP requires Java 8+ to run.
- The Mac OS/X installer comes with Java 8+.
- Linux, Windows, and the various cross-platform versions require installing Java 8+ separately.
- Docker versions do not require installing Java at all.
Determine whether to persist the session
Once you start installing ZAP, you need to specify if you want to persist this ZAP session. ZAP sessions are recorded by default to the disk in an HSQLDB database that gets a default location and name. If you choose not to persist a session, the files are deleted once you exit ZAP.
If you decide to persist this session, all session information is saved within the local database. ZAP lets you provide custom locations and names for saving the files. You can access the database later.
Key components of the desktop user interface (UI)
ZAP’s desktop UI is composed of the following elements:
- Menu Bar—lets you access ZAP’s manual and automated tools.
- Toolbar—provides easy access to commonly used ZAP features.
- Tree Window—displays the Scripts tree and Sites tree.
- Workspace Window—displays responses, scripts, and requests and lets you edit them.
- Information Window—displays the details of manual and automated tools.
- Footer – displays a summary of all alerts and the status of all main automated tools.
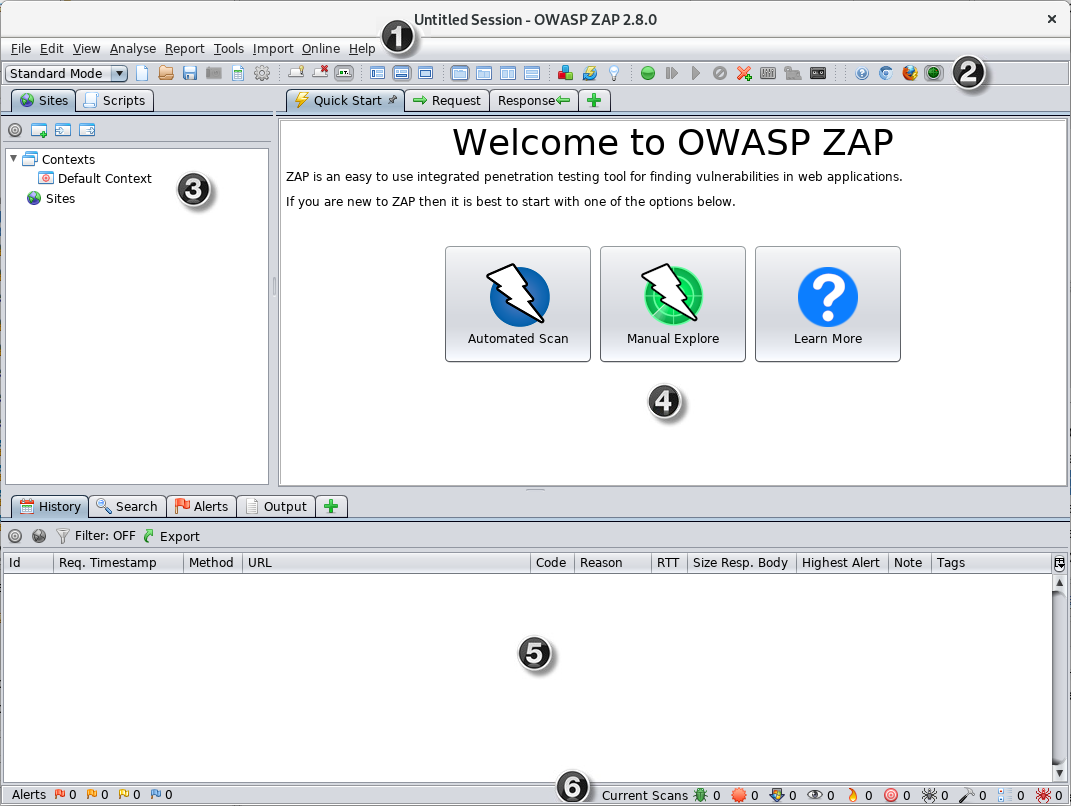
Image Source: OWASP
Using the Quick Start tab
The Quick Start tab is an add-on included with your ZAP installation, which can help you get started with ZAP. Here is how you can run a Quick Start Automated Scan:
- Start ZAP, go to the Workspace Window, select the Quick Start tab, and choose the big Automated Scan button.
- Go to the URL to attack text box, enter the full URL of the web application you intend to attack, and then click the Attack button.
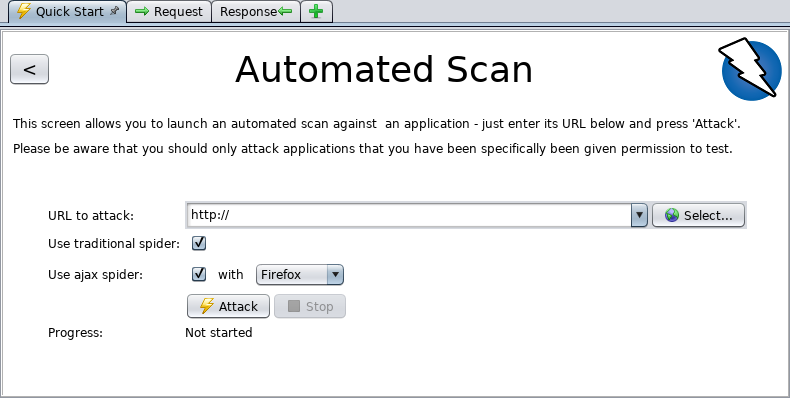
Image Source: OWASP
How ZAP attacks work
Once you click the Attack button, ZAP starts crawling the web application with its spider, passively scanning each page it finds. Next, ZAP uses the active scanner to attack all discovered pages, parameters, and functionality.
ZAP includes two spiders that can crawl web applications. You can use one or both of the spiders. Here are key differences between the spiders:
- A traditional ZAP spider—this spider discovers links by examining the HTML in responses from a web app. It is fast but not always effective when you want to explore AJAX web applications that generate links using JavaScript.
- ZAP’s AJAX spider—this spider is for AJAX applications. It explores a web application by invoking browsers, which then follow all the links that were generated. It is slower than the traditional spider and requires extra configuration when using it in a “headless” environment.
Passive vs. active scanning
ZAP passively scans all responses and requests that are proxied through it. This type of scanning does not change responses, which is why it is generally considered safe. The scanning is performed in a background thread so as not to slow down exploration.
You can use passive scanning to find certain vulnerabilities, get a sense of the basic security state of the tested web application, and find locations requiring further investigation.
ZAP’s active scanning functionality attempts to identify more vulnerabilities. It works using known attacks against the targets. Note that active scanning launches a real attack on the target and might put the target at risk. You should only use active scanning against targets that have given you explicit permission to conduct penetration testing.




