Table of Contents
- What is industry 4.0?
- IoT – Internet of Things
- Blockchain
- AI – Artificial Intelligence
- The Way Forward
In the era referred to as ‘Industry 4.0’ or ‘The Fourth Industrial Revolution,’ two of the pillars of the technology field; automation and data transfer are closely coupled with concerns regarding cybersecurity.
As organizations own, or use more and more information and assets which become additional nodes in the network, the attack surface area increases exponentially. As a result, cybersecurity aspects are transforming at an unprecedented rate. The challenges to security are becoming more prominent than ever, with both sides– hackers and security teams – trying to stay ahead of each other. In today’s hyper-connected world, cyberattacks are no longer a matter of “if”, but rather “when”.
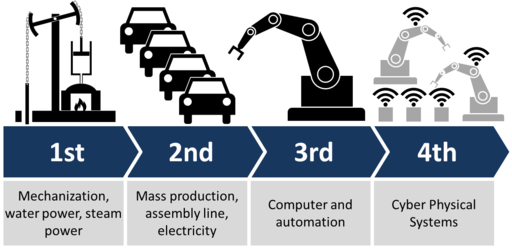
What is industry 4.0?
As the use of computers and automation led the charge through the last few decades, organizations and governments focused their efforts on investments in the IT infrastructure era, which is referred to as ‘Industry 3.0’.
However, today, the focus has shifted to new technologies such as IoT (Internet of Things), AI (Artificial Intelligence), machine learning and reinforcement learning which are defining the new work culture across almost all industries. Industry 4.0 essentially blends automation with advanced AI to reduce direct human effort and resources. The result is a more efficient utilization of both financial and material resources.
In the era of the Fourth Industrial Revolution, organizations are hyper-connected with smart devices and smart networks. This poses a very lucrative target for hackers who can try to exploit the significantly higher number of vulnerable entry points into networks and devices. . Cyberattacks on critical infrastructure and in vital industrial sectors have become more frequent and more sophisticated.

IoT – Internet of Things
Internet of Things describes a world in which smart technologies enable objects within an intelligent network to communicate with each other and interface with humans effortlessly.
This connected world of accessibility and technology does not come without its consequences, as interconnectivity implies hackability. Most of these devices are designed with little to no built in security mechanisms, making them easy targets for security breaches. This new world of convenience calls for new and revolutionary protection measures and strategies to assure secure networks.
Blockchain
As a concept, blockchain has been around for approximately a decade. It is a well understood and defined concept that forms the backbone of most common cryptocurrencies. Blockchain, as a technology, focusses on the integrity and immutability of transactions. While blockchain as a technology is evolving, it offers solutions that can compete with current centralized offerings in terms of speed, but the blockchain is much more reliable considering capacity and trust. Inevitably, in IoT, blockchains will be used to secure infrastructure while maintaining device interoperability.
Although blockchain holds immense promise and potential, it remains vulnerable to cyber threats and risks. A robust cybersecurity program is therefore crucial for protecting blockchain assets from cyber threats.
AI – Artificial Intelligence
Artificial Intelligence is another technology that is rapidly permeating organizations and government departments. It is a branch of computer science that helps to build solutions with human-like intelligence that can carry out complex tasks independently.
AI applications are based on heuristics such as neural networks, machine learning, deep learning and natural language processing algorithms. Machines mimic humans only after they are trained to accomplish specific activities by processing vast amounts of data and identifying patterns in that data. The growing interest in these technologies and the value they offer is resulting in their adoption across many aspects of software and IT..
AI has the potential to make cybersecurity more efficient and responsive to ever-increasing threats and improve the cybersecurity posture of an organization

The Way Forward
The more industries become connected, the more vulnerable they are to the risk of cyberattacks because there are significantly more entry points for hackers to find and exploit. Hackers can target the connected devices that generate data, the networks that carry the data, the servers that host it, or the information systems that use it.
AI has the potential to make cybersecurity more efficient and responsive against ever-increasing threats and improve the cybersecurity posture of organizations. Being the world’s first AI-powered Application Security Testing platform, Bright helps innovative companies that are in the forefront of the Industry 4.0 era significantly reduce cybersecurity risks.
Cybersecurity should never be an obstacle to progress. Bright’s AI powered application security solutions help organizations save time and eliminate the security personnel bottleneck while reducing costs and their exposure window by being secure by design.
To learn more about how you can adopt these tactics in your organization and embrace the fourth industrial revolution, or you have any questions on how to become secured by design contact us today.




















