What is OWASP API Top 10?
APIs are a critical element in modern software development and are central to the digital economy. This also makes APIs a prime target for attackers, because they expose application logic and sensitive data such as personal information (PII).
In response to the rise of API-related security incidents and vulnerabilities in recent years, the Open Web Application Security Project (OWASP), famous for publishing the Top 10 Web Application Vulnerabilities, created a new Top 10 list of API security concerns. The list is based on a rigorous methodology that identifies the security weaknesses most likely to result in a damaging breach.
Related content: Read our guide to OWASP Top 10.
In this article:
OWASP Top 10 API Security Threats
The OWASP API Security Top 10 list is a document that warns against ten critical API security threats and offers mitigation strategies to help avoid these issues.
Broken Object Level Authorization
APIs can expose endpoints handling object identifiers, creating a wider attack surface and access control issues. Here are several practices to help mitigate this threat:
- Implement a system that can detect and correct broken object-level authorization automatically to reduce the damage caused by this issue.
- Configure an authorization mechanism, including object-level authorization checks for each function that can access a data source via user inputs
- Set up an API gateway.
- Use threat modeling to examine existing authorization policies to determine if threat actors can access items by knowing or guessing an object’s ID value.
Broken User Authentication
Misconfigured or vulnerable authentication mechanisms allow threat actors to exploit and compromise systems. Threat actors can use these flaws to do the following:
- Compromise authentication tokens or exploit implementation flaws to take over user identities permanently or temporarily.
- Compromise the system’s ability to identify a client or user
- Compromise the overall API security.
Here are best practices to help avoid broken user authentication:
- Limit the number of login attempts and protect user credentials.
- Use strong API keys and set up a uniform approach for authentication across all API endpoints.
- Implement the relevant authentication techniques recommended by the Application Security Verification Standard (ASVS).
- Enforce a multi-layer authentication process that verifies user identities.
Excessive Data Exposure
Excessive data exposure can occur when you expose all object properties without considering the sensitivity level of each object. It is typically the result of relying on clients to perform data filtering before displaying it to users.
Here are best practices to help avoid excessive data exposure:
- Build security into the API design to limit API’s exposure to various security threats, including excessive data exposure.
- Do not depend on clients to perform data filtering.
- Limit the return response from your back-end system to make it difficult for threat actors to find vulnerabilities.
Lack of Resources & Rate Limiting
Not all APIs restrict the number of resources clients and users can request. Unfortunately, this lack of limitations can severely affect the API server performance, leading to Denial of Service (DoS) or brute force attacks.
Here are best practices to consider when restricting requests:
- Perform threat modeling during design to assess existing rate-limiting controls.
- Use the OWASP Automated Threat Handbook to protect APIs from abuse by bots and automated mechanisms.
Learn more in our detailed guide to owasp mobile top 10.
Broken Function Level Authorization
Broken function-level authorization can allow threat actors to gain unauthorized access to administrative functions or user resources. This authorization flaw is often the result of complex access control policies with various groups, roles, and hierarchies that have an unclear separation between regular and administrative functions.
Here are best practices to help avoid broken function-level authorization:
- Create and implement a well-defined policy that defines the roles and level of access allowed to users. This policy can help ensure everyone understands their responsibilities and the consequences of violating this policy.
- Regularly audit the system to ensure all access controls remain effective and verify that unauthorized users have not gained access.
Mass Assignment
Mass assignment occurs when you bind client-provided data, like JSON, to data models without using allowlist-based properties filtering to secure the process. It can allow threat actors to guess object properties, explore other API endpoints, read the documentation, or add object properties into request payloads.
Here are best practices to help avoid mass assignment:
- Employ penetration testing (pentesting) to identify vulnerabilities that external actors can exploit, such as mass assignment.
- Avoid directly mapping client inputs to internal input variables.
- Create an allowlist of properties that a client is authorized to access and ensure only clients with the proper privileges are granted access to the API response.
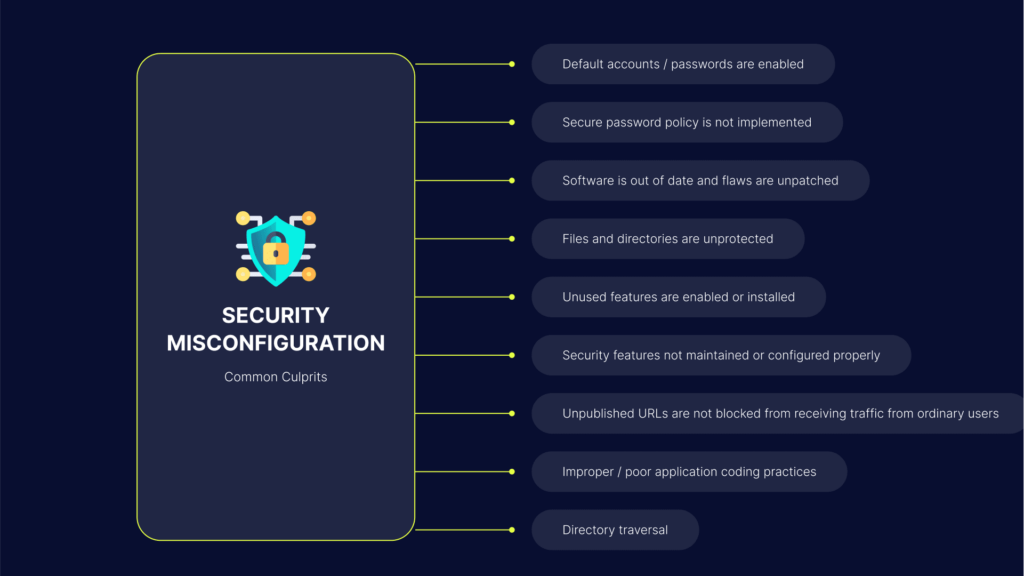
Security Misconfiguration
Security misconfigurations is an umbrella term that encompasses various issues, including:
- Incomplete or ad-hoc configurations
- Insecure default configurations
- Open cloud storage
- Unnecessary HTTP methods
- Misconfigured HTTP headers
- Verbose error messages that contain sensitive information
- Permissive cross-origin resource sharing (CORS)
Here are best practices to help avoid security misconfigurations:
- Perform periodic security audits to identify misconfigurations or missing patches.
- Never rely on default configurations.
- Use automated scanners and human reviews to test the entire stack for security misconfigurations.
- Do not include sensitive data in error messages.
Injection
Injection flaws occur when a query or command sends untrusted data to an interpreter. If the untrusted data is malicious, it can manipulate the interpreter to execute unauthorized commands or access data without authorization. Common attacks include SQL injection (SQLi), NoSQL injection, and command injection.
Here are best practices to help avoid injection flaws:
- Use allowlists to perform input validation for all inputs.
- Set up a parameterized interface for inbound API requests.
- Ensure the query interface limits the number of returned records.
Improper Assets Management
Since APIs expose many endpoints, it is critical to maintain and update clearly defined documentation. Deprecated API versions or exposed debug endpoints can allow threat actors to hack your systems.
Here are best practices to help avoid improper assets management:
- Inventory your APIs across all environments, including production, testing, development, and staging.
- Regularly review all APIs for security, emphasizing the standardization of functions.
- Stack rank all APIs by risk levels and then improve the security functions of the riskiest items.
Insufficient Logging & Monitoring
Logging and monitoring are key components of incident response and forensics. Monitoring provides visibility, and logging provides the data needed to detect and investigate threats. Insufficient monitoring and logging hinder visibility, and ineffective or missing integration with incident response severely hinders your ability to protect against cyberattacks.
This threat can allow malicious actors to attack systems, pivot to other systems, maintain persistence, and extract, destroy, or modify data.
Here are best practices to help avoid insufficient monitoring and logging:
- Use a standard logging format across all APIs to ensure the efficiency of future incident response efforts.
- Monitor API endpoints across all software development stages and respond to the security issues identified in APIs.
OWASP API Top 10 with Bright Security
Bright Security offers a dev first approach to testing your web applications, with a specific focus on API security testing.
With support for a wide range of API architectures, it automatically tests both legacy and modern applications, including REST, SOAP, and GraphQL APIs.
Bright Security integrates with DevOps and CI/CD toolsets, allowing developers to detect and fix vulnerabilities on every build. It reduces the reliance on manual testing by leveraging multiple discovery methods:
- HAR files
- OpenAPI (Swagger) files
- Postman Collections
Start detecting the technical OWASP API Top 10 and more, seamlessly integrated across your pipelines via:
- Bright Security Rest API
- Convenient CLI for developers
- Common DevOps tools like CircleCI, Jenkins, JIRA, GitHub, Azure DevOps, and more